CS204 - Cyber Law
2
Topics
23
Posts
Re: CS204 Assignment 2 Solution and Discussion
Assignment No. 02
Semester:Spring 2020
Cyber Law – CS204
Total Marks: 15
Due Date:16/06/2020
Objective:
• The objective of this assignment is to enhance the knowledge of the students about cryptography technique for security purposes and cyber security measures.
Uploading instructions:
• Your assignment must be in .doc or .docx format (Any other formats like scan images, pdf, bmp, etc will not be accepted).
• Save your assignment with your ID (e.g. bc020200786.doc).
• No assignment will be accepted through email.
Rules for Marking:
It should be clear that your assignment will not get any credit if:
• The assignment is submitted after due date.
• The submitted assignment does not open or file is corrupted.
• Your assignment is copied from internet, handouts or from any other student
• Assignment is covered from lectures 04 to 06.
For any query about the assignment, contact at cs204@vu.edu.pk
Assignment Questions
Questions: Marks 15
Question.1 (10 Marks)
Use the caesar cipher method to encrypt the following words with shift key of 3 and show the complete process step by step.
• “ASSIGNMENT”
• “TOOLS”
Question. 2 (5 Marks)
Suppose that if you’ve ever tried to login to your online bank account and find that not all of your savings are being accounted for, it could be an indication that you’ve been targeted by cyber criminal. Although there are several ways that cyber criminals could have gotten your account data, there’s a fair chance you’ve accidentally come across a phishing website in the past, misinterpreting the login page of your online bank. Enlist all possible security measures to protect your online banking account from cyber criminals.
Best of Luck
Re: CS204 Assignment 1 Solution and Discussion
Assignment No. 01
Semester:Spring 2020
Cyber Law – CS204
Total Marks: 15
Due Date:29/05/2020
OBJECTIVE:
The objective of this assignment is to enhance the knowledge of the students about E-commerce business models ,cyber crime, cyber crime catagories and cyber crime security measures.
Uploading instructions:
• Your assignment must be in .doc or .docx format (Any other formats like scan images, pdf, bmp, etc will not be accepted).
• Save your assignment with your ID (e.g. bc020200786.doc).
• No assignment will be accepted through email.
Rules for Marking:
It should be clear that your assignment will not get any credit if:
• The assignment is submitted after due date.
• The submitted assignment does not open or file is corrupted.
• Your assignment is copied from internet, handouts or from any other student
• Assignment is covered from lectures 01 to 03.
For any query about the assignment, contact at cs204@vu.edu.pk
Assignment Questions
Questions: Marks 1555
Question. 1 Marks 05
Visit each of the sites below and then place them into one of the four E-commerce business model (s) according to their primary focus:
www.newrelic.com
www.bulkbookstore.com
www.mcdelivery.com.pk
www.uber.com
www.olx.com.pk
Question. 2 Marks 10
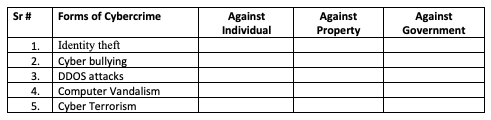
Mr. “Omar” is an HR coordinator at XYZ University. He receives an E-mail containing a message that, “Your University’s E-mail account password will be expired within 24 hours” from some fake E-mail account pretending to be the legitimate E-mail from University. Mr. “Omar” is redirected to a fake password renewal page i.e.“xyzcuniversity.edurenewal.com” where both new and existing passwords are requested. The cyber attacker is monitoring the page and hacks the original password to gain access.
Keeping in view the above scenario, answer the following questions:
Mention the cyber-crime name, which is occurring in the scenario.
Mention the category of cyber-crime.
Mention all possible prevention measures for such type of cyber-crimes.
Best of Luck
Assignment No. 03
Semester: Fall 2019
Cyber Law – CS204
Total Marks: 15
Due Date:27/01/2020
Objectives:
The objective of this assignment is to enhance the learning capabilities of the student about:
• The Intellectual Property Rights
• Investigation and Prosecution Agencies.
• Power of Officers
Instructions:
Please read the following instructions carefully before submitting the assignment:
You will submit your assignment before or on due date on VU-LMS.
Assignment sent via Email will not be accepted/graded in any case.
If the submitted assignment does not open or file is corrupt, it will not be graded.
Assignment should be completed by your own efforts it should not be copied from internet, handouts or books.
You will submit solution only in the Microsoft Word File.
Assignment is covered from lectures 09 to 12.
For any query about the assignment, contact at cs204@vu.edu.pk
Assignment Questions
Questions: Marks 15
Question. 1 (05 Marks)
E-Series is an online music streaming website which has launched several music albums under its banner name and have all the copyrights reserved for its content.
This company has published its music on online streaming website but from there other creators have illegally copied and molded the content of E-series and also uploaded with their own name.
E-series took the notice and the case is now sent to National Response Centre For Cyber Crimes for further investigation.
After reading the above scenario answer the following Question:
Which personnel shall have the authority to obtain and copy the data, use equipment to make copies and obtain an intelligible output from the information system of online streaming website? And Under which Cybercrime Act this authority is delegated to the said personnel.
Question. 2 (10 Marks)
Identify the most suitable Intellectual Property Right for each of the following case:
A cricketer creates his own company to sell his own collection of clothes. What kind of intellectual property can he use to show that his company is making the clothes?
Which sort of intellectual property gives you the right to determine who can make and sell copies of your work if you write an original story?
If a corporation develops a new idea that boosts its main product, what kind of intellectual property will it use to prohibit others from stealing its invention?
Which term describes a logo or sign that identifies a brand?
Which intellectual property protection applies for :Getz pharmaceutical
Best of Luck
Assignment No. 02
Semester: Fall 2019
Cyber Law – CS204
Total Marks: 15
Due Date:02/12/2019
Objective:
The objective of this assignment is to understand the concept of cyber security, its need, major security problems and the usage of cryptography technique for security purposes.
Instructions:
Please read the following instructions carefully before submitting the assignment:
You will submit your assignment before or on due date on VU-LMS.
Assignment sent via Email will not be accepted/graded in any case.
If the submitted assignment does not open or file is corrupt, it will not be graded.
Assignment should be completed by your own efforts it should not be copied from internet, handouts or books.
You will submit solution only in the Microsoft Word File.
Assignment is covered from lectures 04 to 06.
For any query about the assignment, contact at cs204@vu.edu.pk
Assignment Questions
Questions: Marks 15
Question. 1 (05 Marks)
Read the following scenario carefully and answer the questions.
An employee of XYZ company get subscription to some number of free online IT magazines. During the process of registration for subscription, some information was being asked by the IT magzines in the form of questions, The IT magzines demand for bank details, first magazine asked for his complete date of birth, the second magazine asked for his bank name, and a third asked for his mother’s name.You are required to identify the possible cyber crime going on there also mention at least one prevention measure?
Question.2 (10 Marks)
Use the caesar cipher method to encrypt the word “ACTIVATION” and show the complete process step by step.
Best of Luck
Graded Discussion Board
Semester: Spring 2019
Cyber Law – CS204
Topic: Cryptography
Scenario
Let us consider that a security company has around 400 employees exchanging valuable sensitive information everyday through internet between offices stationed at Karachi and Islamabad.
Mohammad Ali is an IT Manager who oversees the overall IT infrastructure and is responsible for implementing the security measures and policies to guarantee the delivery of the messages safely so that no one can breach the confidential information.
To achieve Privacy and high security normally the information is encrypted using symmetric and asymmetric encryptions, however there are some advantages and disadvantages of using both techniques in the above scenario.
Point of Discussion:
If you are asked to choose the best encryption technique (i.e. Symmetric or asymmetric) in the above scenario then what will be your choice? Support your answer with solid reasons considering the pros and cons of both techniques.
Best of Luck !